How to Write an ISO 27001 Information Security Policy + Free Template [Updated for ISO 27001:2022]
Emily Bonnie
Cavan Leung
ISO/IEC 27001 requires organizations to create and maintain dozens of policies to show how your organization protects data and mitigates risk. Of these dozens of policies, one of the most important is the ISO 27001 information security policy.
Discover what this policy is, why it's important, and best practices for writing your ISO 27001 information security policy. Plus, get an auditor-approved ISO 27001 information security policy template with all the legwork done for you.
What is an ISO 27001 information security policy?
An ISO 27001 information security policy essentially provides an overview of how your company approaches data security. More specifically, it sets standards for the acceptable use of an organization’s information systems and technology, from networks and databases to software applications. And it defines rules and processes for protecting data confidentiality, integrity, and availability (often abbreviated as CIA).
1. Confidentiality: Protecting confidential information by limiting its access, storage, and use
Your information security policy should explain how you control access to information and how you prevent data breaches and leaks.
2. Integrity: Verifying that company systems operate as intended
When writing your information security policy, you should think about how you establish change control processes, keep unauthorized users from changing information, prevent human error, and ensure technology is configured properly to avoid errors.
3. Availability: Ensuring employees and clients can rely on your systems to do their work
Your information security policy needs to discuss how you ensure data availability, including how you account for natural disasters and storage erosion, how you protect domain integrity, etc.
Recommended reading

What is ISO 27001 Certification & Its Purpose?
Why is the ISO 27001 information security policy important?
An information security policy (consisting of low-level policies and a high-level summary) that explains how management approaches information security is required in the ISO 27001 standard.
But ISO 27001 information security policies don't exist just to check off a box on a list of compliance tasks and framework requirements. They may seem like a bunch of formal documents to stick in a file that nobody will ever actually use, except maybe your information security auditor or someone in HR once a year. But this couldn't be further from the truth.
ISO 27001 information security policies are how you explain exactly what you do to protect the confidentiality, integrity, and availability of sensitive data — to your employees, vendors, partners, customers, and auditors. Here's a few key reasons that's important:
- Clarity and consistency around information security management: A well-written ISO 27001 information security policy establishes a shared understanding of how information security is handled across your organization. That means employees know what’s expected of them, vendors and partners understand requirements, and customers gain confidence in your ability to safeguard sensitive information.
- Foundation of the ISMS: This policy serves as the backbone of your information security management system (ISMS). It defines the guiding principles for managing risks, protecting assets, and complying with regulations.
- Operational alignment: By setting clear objectives and assigning responsibilities, the ISO 27001 information security policy helps ensure that information security isn’t siloed. It’s integrated into daily business operations and decision-making, and is everyone's responsibility.
- Audit readiness: During an ISO 27001 audit, this policy is often one of the first documents reviewed. It demonstrates leadership’s commitment to information security and provides evidence that your ISMS is properly designed and maintained.
Now that we understand the importance of the ISO 27001 information security policy, let's take a closer look at the standard's requirements to understand how to create and maintain one.
Recommended reading
ISO 27001 Checklist: Your 14-Step Roadmap for Becoming ISO Certified
ISO 27001 Information Security Policy requirements: Clause 5.2 and Annex A 5.1
In the latest version of ISO 27001, Clause 5.2 requires that top management establish a set of information security policies and Annex A control 5.1 requires organizations to establish, regularly review, and communicate these policies to employees and third-party users.
All of these policies are summarized into a high-level master information security policy, which outlines the organization’s overall approach to information security and asset management.
According to Clause 5.2 and Annex A 5.1 (as well other Annex A controls like 6.1, 6.3, and 18.1) of the ISO 27001 standard, this policy must:
- Be tailored to the organization
- Demonstrate management’s commitment to the ISO 27001 ISMS
- Define how information security objectives are proposed, reviewed, and approved
- Be communicated to employees, stakeholders, and other interested parties, such as vendors and business partners
- Have a defined owner who is responsible for keeping the policy up to date
- Be reviewed on a regular basis (at least annually), or when significant changes occur such as changes to information security controls, technologies, legislation, or business/management processes
- Be informed by business needs and any applicable regulations or legal requirements affecting the organization, such as HIPAA and GDPR
- Be used as the foundation for the organization's information security awareness, education, and training programs

Recommended reading

ISO 27001 Controls Explained: A Guide to Annex A
Did information security policy requirements change in the ISO 27001:2022 update?
The newest version of the international standard, ISO/IEC 27001:2022, introduced several key changes. While the core requirements and controls related to the information security policy remain the same, there are a few important changes to be aware of:
- Clause alignment: The requirement for an information security policy is now located in Clause 5.2 of the 2022 standard (previously only referenced in Annex A of ISO 27001:2013). This shift underscores its importance as a core management system requirement, not just a control.
- Integration with business context: The 2022 revision places greater emphasis on tailoring your policy to the organization’s unique context, stakeholders, and risk environment. A generic policy is not sufficient. Auditors will expect to see alignment with your actual ISMS scope, business goals, and applicable regulations.
- Annex A control updates: Annex A was significantly restructured in ISO 27001:2022, changing from 114 controls divided into 14 domains in the 2013 version to 93 controls grouped into 4 clauses or themes. This reduced number reflects a substantial amount of controls that were merged in the 2022 version, including Annex A control 5.1 Policies for information security, which was previously split into 5.1.1 and 5.1.2. Your information security policy should now reference and support this updated control structure.
- Attributes and modernization: The 2022 update introduced attributes to provide additional lenses to view and categorize controls with, such as their operational capabilities, security properties, and cybersecurity concepts. While not mandatory, aligning your information security policy language with these attributes can help demonstrate maturity and modern thinking around security.
- Ongoing review expectations: While reviews were always required, ISO 27001:2022 audits place more emphasis on whether organizations can show evidence that the information security policy is reviewed at least annually and whenever significant changes (like new technologies, business processes, or threats) occur.
Takeaway: If your organization created its information security policy under ISO 27001:2013, now is the time to review and update it. Updating language, references, and alignment with the 2022 requirements and controls will ensure your ISMS remains compliant and audit-ready.
Recommended reading

ISO 27001:2022 and ISO 27002:2022 Explained: How to Comply Before October 2025 Deadline
ISO 27001 Information Security Policy template
We've created an ISO 27001 Information Security Policy Template to show you what this policy might include, how it might be organized, and how long it may be to meet the ISO 27001 requirements and controls above.
Downloading and reviewing this template can help you, whether you're preparing for an audit or just determining if ISO 27001 compliance is the right choice for your organization.

Download the ISO 27001 Information Security Policy template
Use this auditor-approved template and then tailor it to your organization to meet the ISO 27001 5.2 requirement.
What should be in an ISO 27001 information security policy?
Oftentimes, people think their information security policy needs to include every single thing about their organization’s cybersecurity and data protection practices. But that’s not the case. The information security policy should be written to achieve three things:
- Force management to thoughtfully consider their goals for information and IT security
- Formalize management’s commitment to continual improvement of the ISMS
- Provide a general overview of the ISMS so that management understands how it works without having to track the minute details of every information security risk assessment, access control, or internal audit. They know what the ISMS is designed to do, how it works, and who is responsible for it.
To achieve these three objectives, here’s what’s typically covered in an ISO 27001 information security policy.
ISO 27001 information security policy outline
Note: This outline is provided for informational purposes only and is not intended as compliance or legal advice. Always consult a legal or compliance professional to verify compliance with applicable laws, regulations, and standards.
I. Purpose
- Define the purpose of the organization’s information security policy
- Example: “The purpose of this policy is to define the organization’s approach to information security and establish responsibilities for protecting data.”
II. Scope
- Define what systems, data, people, and locations are covered by the ISMS.
- Clarify exclusions (if any).
- Example: "This policy applies to all employees and contractors."
III. Information Security Principles
- Outline the guiding principles your organization follows (e.g., risk-based approach, least privilege, continual improvement).
- Example: "Information security is managed based on risk, legal and regulatory requirements, and business needs."
IV. Information Security Objectives
- State high-level goals such as ensuring confidentiality, integrity, and availability (CIA) of information assets.
- Example: "To provide the resources required to develop, implement, and continually improve the information security management system (ISMS)."
V. Roles & Responsibilities
- Specify who is responsible for implementing, maintaining, and monitoring performance of the ISMS
- Example: "The Information Security Management Systems Manager has the overall responsibility for ensuring that the ISMS conforms to the requirements of the ISO 27001 standard."
VI. Requirements
- List any applicable legal, contractual, or regulatory requirements that relate to your ISMS (such as HIPAA, GDPR, CPRA, DORA, etc.)
- Example: "[Organization Name] takes its legal and regulatory obligations seriously. These requirements are recorded in the Legal and Contactual Requirements Register [or other Document Name]."
VII. Communication
- Clarify who the policy needs to be shared with, internally or with contractors and third-party vendors (if applicable)
- Example: "Policies are made readily and easily available to all employees and contractors. A training and communication plan is in place to communicate the policies, process, and concepts of information security."
VIII. Support
- Define the resources and supplemental policies that will support information security (e.g., Acceptable Use Policy, Data Retention Policy)
- Example: "The information security management system (ISMS) is built on an information security policy framework, which is made up of the following policies: [bulleted list]."
VIIII. Review and maintenance
- Specify that the policy will be reviewed at least annually or after significant organizational or regulatory changes
- Example: "The policy is updated and reviewed on an annual basis as part of the process for continual improvement."
Our team of experienced auditors and compliance specialists shared their essential tips and best practices for writing an information security policy that meets ISO 27001 requirements.
- Assign an owner who’s responsible for keeping the information security policy up to date and ensuring it gets reviewed at least annually.
- Corrective changes and updates should be recorded and approved following senior management review.
- Label your ISO 27001 information security policy and other policies and procedures with a a predefined classification matrix.
- The auditor will likely review the information security policy and evidence of employee review/acceptance during the Stage 1 audit and then interview management and other key stakeholders to verify that there is a regular process in place to disseminate, review, and update this and other policies during the Stage 2 audit.
Recommended reading

5 Tips for Preparing for ISO 27001 Certification From Real Auditors
ISO 27001 information security policy vs procedures
Organizations often confuse the ISO 27001 information security policy with actual security procedures. While they’re closely related, they serve different functions and purposes in your ISMS.
- The ISO 27001 information security policy is high-level and strategic. It defines your organization’s overall approach to protecting data, outlines objectives, and sets expectations for employees and third parties. Think of it as the “what” and “why” behind your ISMS.
- ISO 27001 information security procedures are detailed and tactical. They describe exactly “how” data is handled securely across your organization. For example, your policy may state that “all employees must use strong passwords and multi-factor authentication,” while a procedure will walk through step-by-step instructions for configuring MFA or creating a compliant password.
Both are essential: the information security policy provides the direction and accountability, while procedures translate those principles into specific actions that keep information secure. Together, they ensure your ISMS is both operationally effective and audit-ready.
The Ultimate Guide to ISO 27001
Creating and maintaining an InfoSec policy is just one ISO 27001 requirement. If you’re looking to meet all the requirements to build and maintain a compliant ISMS and achieve ISO 27001 certification, this guide has all the details you need to get started.
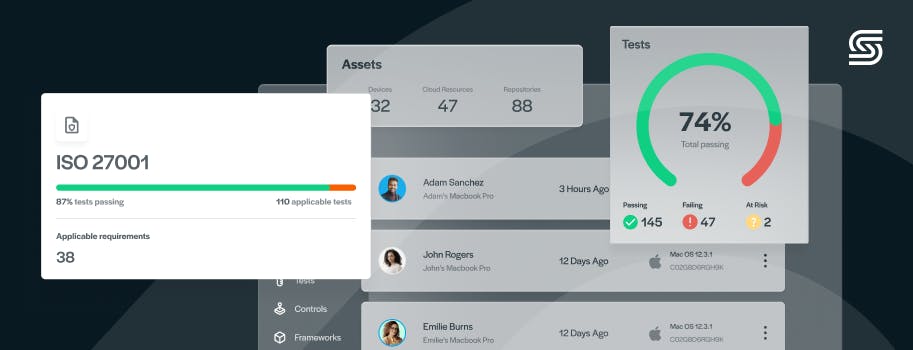
Quickly create ISO 27001 policies with Secureframe
The information security policy is just the tip of the iceberg for the ISO 27001 standard, which has 25 base policies. With Secureframe, you can save yourself a ton of time and effort with our policy library and automated workflows. Get 40+ policy templates written by compliance experts and vetted by dozens of auditors, ready for you to customize for your business. We can also help you save hundreds of hours and thousands of dollars on audit preparation and consultant fees by automating evidence collection, continuous monitoring, risk assessments, control remediation, and more.
Request a demo to learn more about how our compliance automation platform can streamline ISO 27001 certification.
This post was originally published in January 2023 and has been updated for comprehensiveness.
Use trust to accelerate growth
FAQs
What are the 3 key elements of information security in ISO 27001?
ISO/IEC 27001:2022 (formerly ISO/IEC 27001:2013) is an international standard that covers 3 elements of information security:
- Confidentiality: Data can only be accessed by authorized users
- Integrity: Data can only be modified or deleted by authorized users
- Availability: Data must be accessible to authorized users when needed
Which clause of ISO 27001 includes requirements related to information security policy?
Clause 5.2 of the ISO 27001 standard includes requirements for top management to establish an information security policy that:
- Is relevant to the purpose of the organization
- Demonstrates management’s commitment to the ISO 27001 ISMS
- Defines how information security objectives are proposed, reviewed, and approved
- Defines an owner who is responsible for keeping the policy up to date
- Is reviewed on a regular basis (at least annually), or when significant changes occur such as changes to information security controls, information technologies, supplier relationships, legislation, or business/management processes
- Is shared and communicated with employees, third-party users, and other interested parties as needed
What is ISO 27001 5.1: Policies for Information Security?
ISO 27001 Annex A control 5.1 details more requirements for the information security policies organizations need to have in place. These policies must be:
- Tailored to the organization, approved by management, and communicated to employees and third-party users
- Led by business needs and address any applicable regulations or legal requirements affecting the organization, such as HIPAA and GDPR
- An important part of the employee education and security awareness training program
- Summarized into a high-level master information security policy
Who should approve and own the ISO 27001 policy?
The ISO 27001 information security policy must be approved by top management to demonstrate leadership’s commitment to the ISMS. A designated owner—often the CISO, security manager, or another senior leader—is responsible for maintaining the policy, ensuring it’s reviewed regularly, and keeping it aligned with business and regulatory requirements.
How long should an ISO 27001 information security policy be?
There’s no required length for an ISO 27001 information security policy. Most are 2–5 pages, long enough to define objectives, scope, roles, and responsibilities but short enough to provide a high-level overview of their approach to information security management. To keep the length down, the information security policy references supporting procedures and policies for specifics.